What Is Two-Factor Authentication (2FA)?
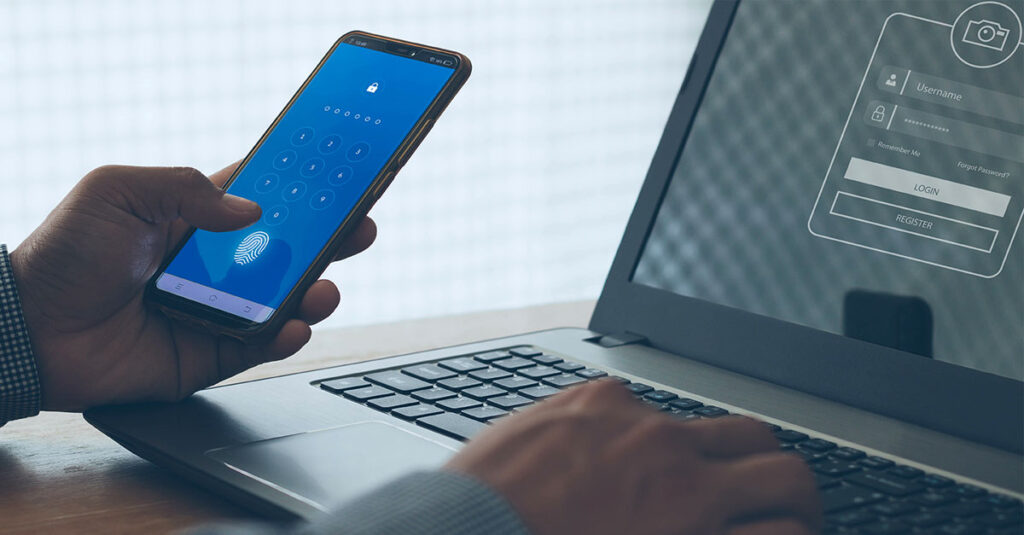
A lot of times these days, you’ll be asked to take an extra step to verify that you’re really you when you sign into your online accounts. It might seem like a hassle, but it’s a good thing. It’s called two-factor authentication (2FA) or multifactor authentication. And you can use it to sign into accounts or onto your personal devices like your phone, tablet or gaming gear.
Even though you have strong passwords, sometimes cybercriminals can hack your password. Time to learn more about why you should be happy about 2FA’s extra layer of protection.
How does two-factor authentication (2FA) work?
2FA requires you to confirm your identity twice when signing into accounts or signing onto your devices. First, you confirm your identity using the correct login credentials. By using 2FA, you provide a second way to verify yourself.
There are three methods of this extra authentication:
- Something you know – The most common authentication is using something only you would know. It can be anything from a PIN code to an answer to a security question.
- Something you own – Your account connects with an email address or phone number. You can prove you’re the account owner by verifying you have access to the email or phone number. One example is a website that sends a security code to your email address or via text to your smartphone. You then enter the code into the website to verify your identity.
- Something you are – Nothing is more unique than your biometrics. People use their fingerprint or facial recognition as a 2FA method for their smartphones and other devices.
2FA may seem like an unnecessary step to access your accounts. But it provides an extra barrier to prevent your account from getting hacked.
Even if a hacker manages to find or guess your password, they’ll have difficulty cracking the 2FA. Because 2FA uses more personal information to verify your identity, it’s harder for hackers to guess or steal it.
How do I turn on 2FA?
It’s smart to add 2FA to your sign-in process. Turning on 2FA is usually simple to do. Check the directions for each of your devices. Sometimes, enabling 2FA is part of the account setup. Other times, you need to manually enable 2FA. To do so, you normally go to your Settings, then to a password or security page, where you can enable 2FA. At this point, you select which method you want to enable. Your choices are usually:
- Authentication app – Popular choices include Google Authenticator or Microsoft Authenticator. The app will provide you with a time-based one-time security code.
- Email – Use your email address to receive a security code.
- SMS – You can receive a security code via text message.
What is the difference between 2FA and MFA?
You’ll often hear 2FA and multifactor authentication (MFA) used interchangeably. The difference is the number of times you verify your identity.
With 2FA, you only verify your identity twice. Using MFA, you will need to verify your identity two or even three times before accessing an account. 2FA falls under the umbrella of MFA, but MFA isn’t always 2FA.
How can I keep 2FA secure?
This extra protection does a lot to prevent hackers from gaining access to your accounts and devices. Still, you have to stay alert and be smart about how you manage your information online. Cybercriminals have found some ways to intercept 2FA using methods like these:
- Researching you – Do you post your life publicly on the internet? Be careful what you share. Hackers could take a look and find the answers to your security questions.
- Posing as a trusted source – Hackers may call you and pretend to be your bank, for example. Then they ask for your 2FA code, which you may hand over thinking it’s a trusted person.
- SIM swapping – Hackers convince mobile phone carriers to activate a fraudulent SIM card with the victim’s phone number. Then the hackers will receive any 2FA codes you’ve sent to your phone, and use those codes to log into your online accounts, like your bank.
- Malware – Hackers may trick you into downloading fake apps on your phone. When you open them, you inadvertently give hackers access to your incoming texts, which might contain 2FA codes to your personal online accounts.
The good news is that awareness can help prevent these hacking methods. It will help you take the necessary steps to avoid falling victim to these scams. At the end of the day, 2FA remains a best practice to secure your account from hackers.
The future of 2FA: Passkeys
Strong passwords and 2FA are the current standard for keeping your accounts secure. But in the near future, passwordless (password-free) authentication will replace passwords and 2FA and change the way we sign onto accounts and devices.
The idea is, your device will store a credential called a passkey. Then the passkey can open and unlock all your online accounts. Apple, Google and Microsoft have all combined efforts to create this passwordless sign-in process.
Always start with a strong password
Passwordless authentication may be the future, but for now, you should concentrate on strong passwords for all of your accounts. There are a few best practices for creating a password that is not likely to get hacked:
- Never use the same password for different accounts. If one account gets hacked, then the other accounts are more at risk of getting hacked as well.
- Create complex passwords. Use the most characters possible and include numbers and symbols.
- Keep passwords confidential. Don’t save them on a file on your computer or a note by your keyboard. You may want to consider using a password manager to safely store and encrypt your passwords.
Frontier Fiber is built for the way you live today—and tomorrow
If you’re still on the lookout for the right ultrafast internet connection for streaming, gaming, working from home and running your smart home—all with enough bandwidth for everyone—find out about Frontier Fiber. Frontier Fiber is available in select areas—check here to see when it’s available at your address.


Join the conversation